Radford University
Artis College of Science and Technology
Innovation and Discovery

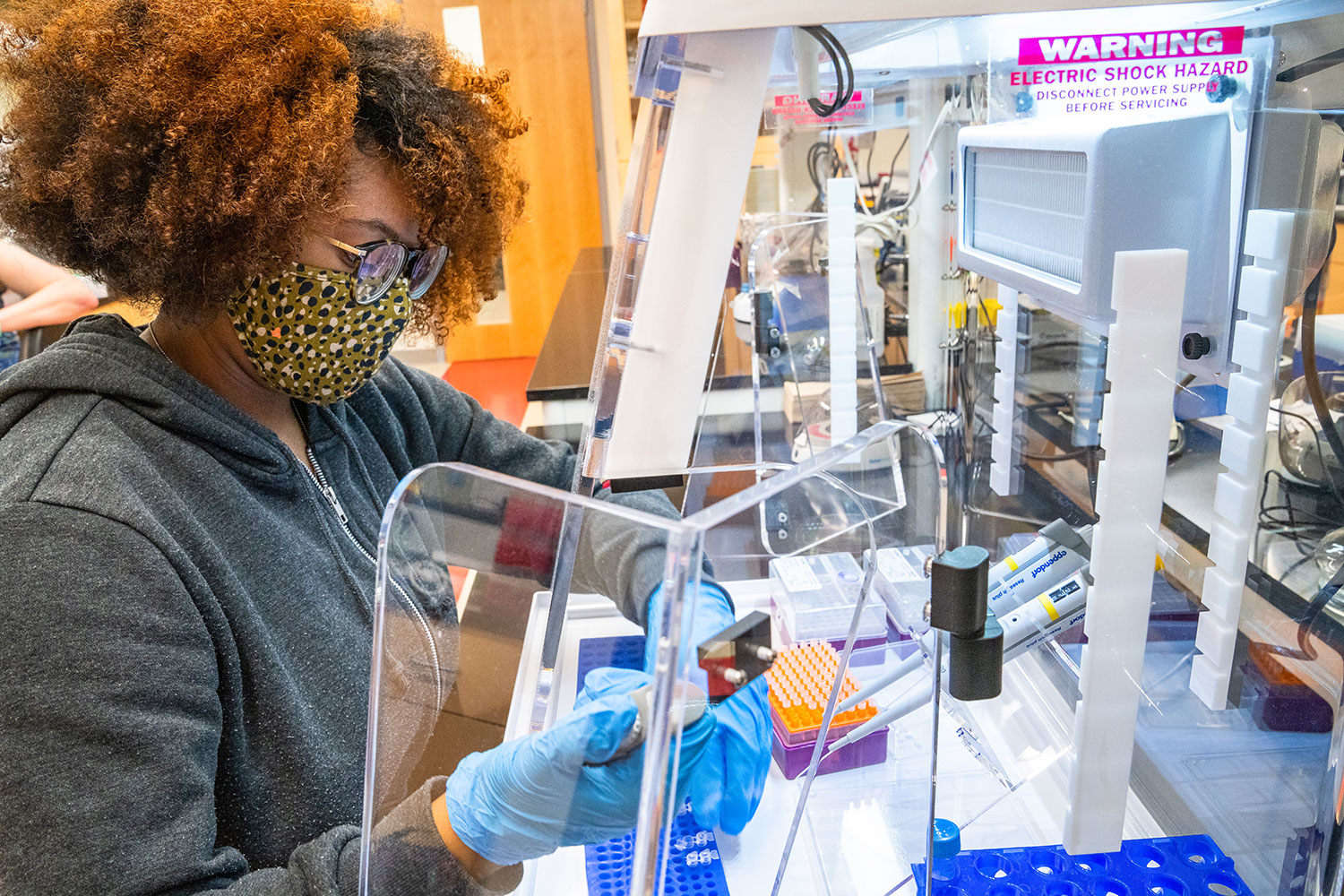
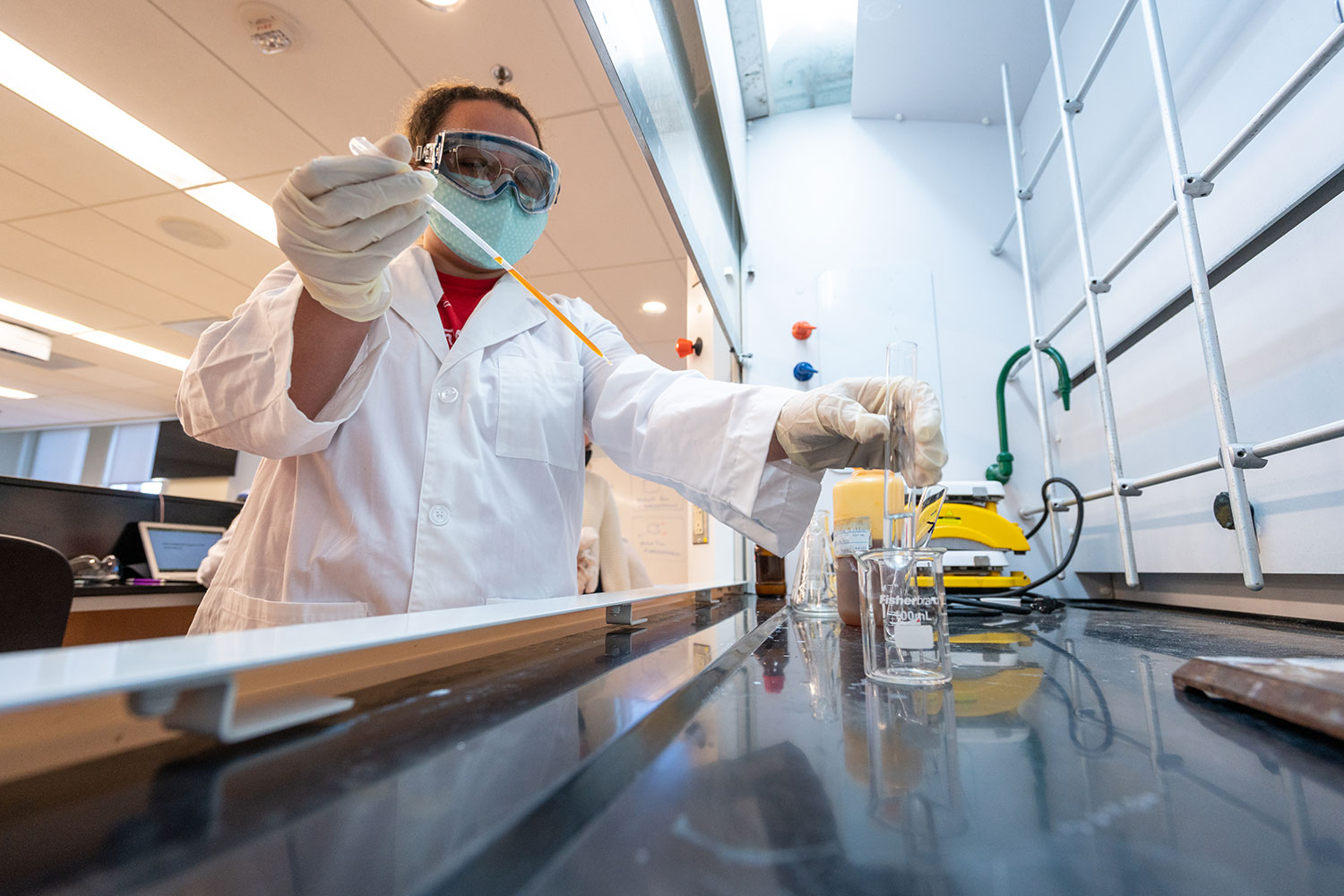
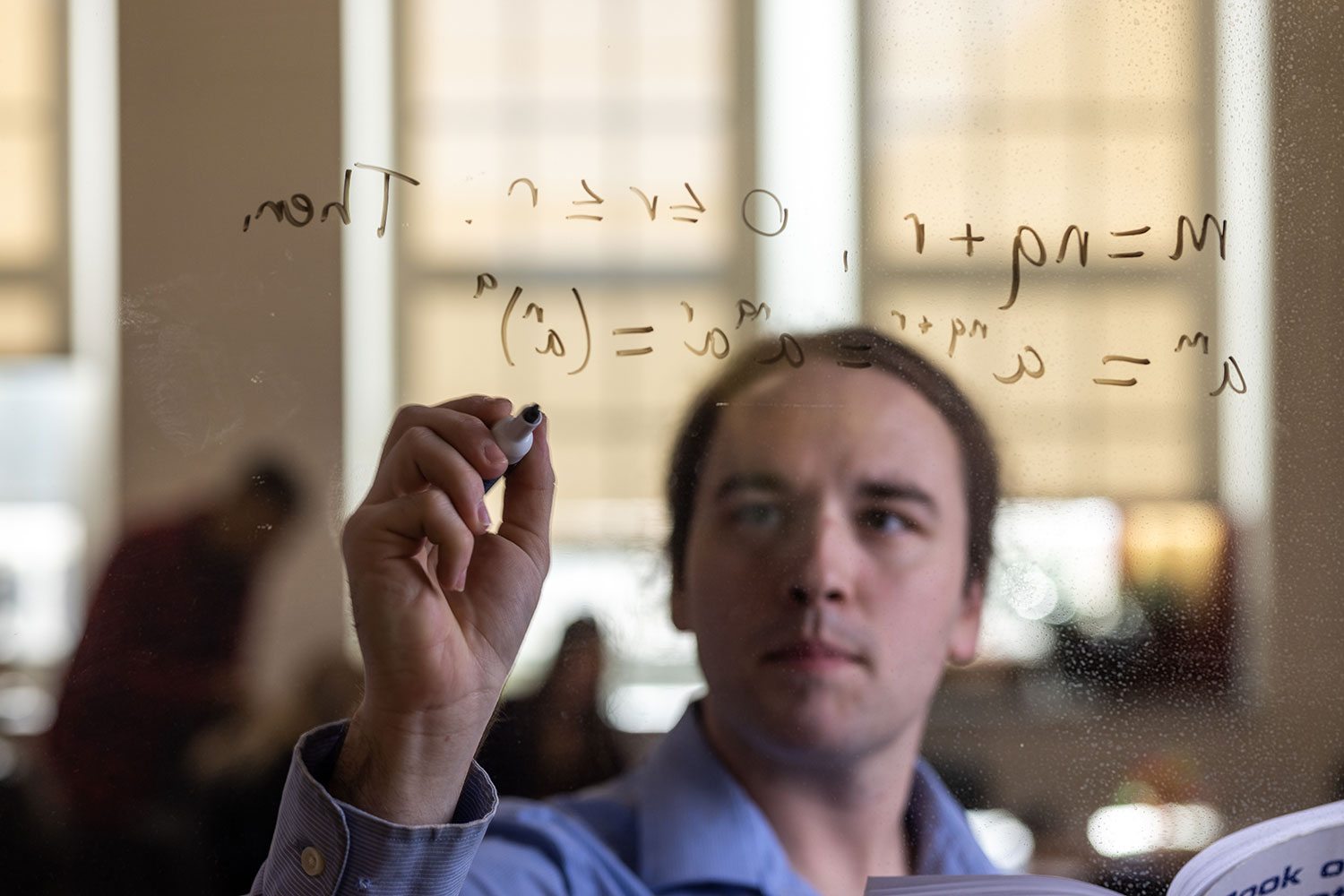
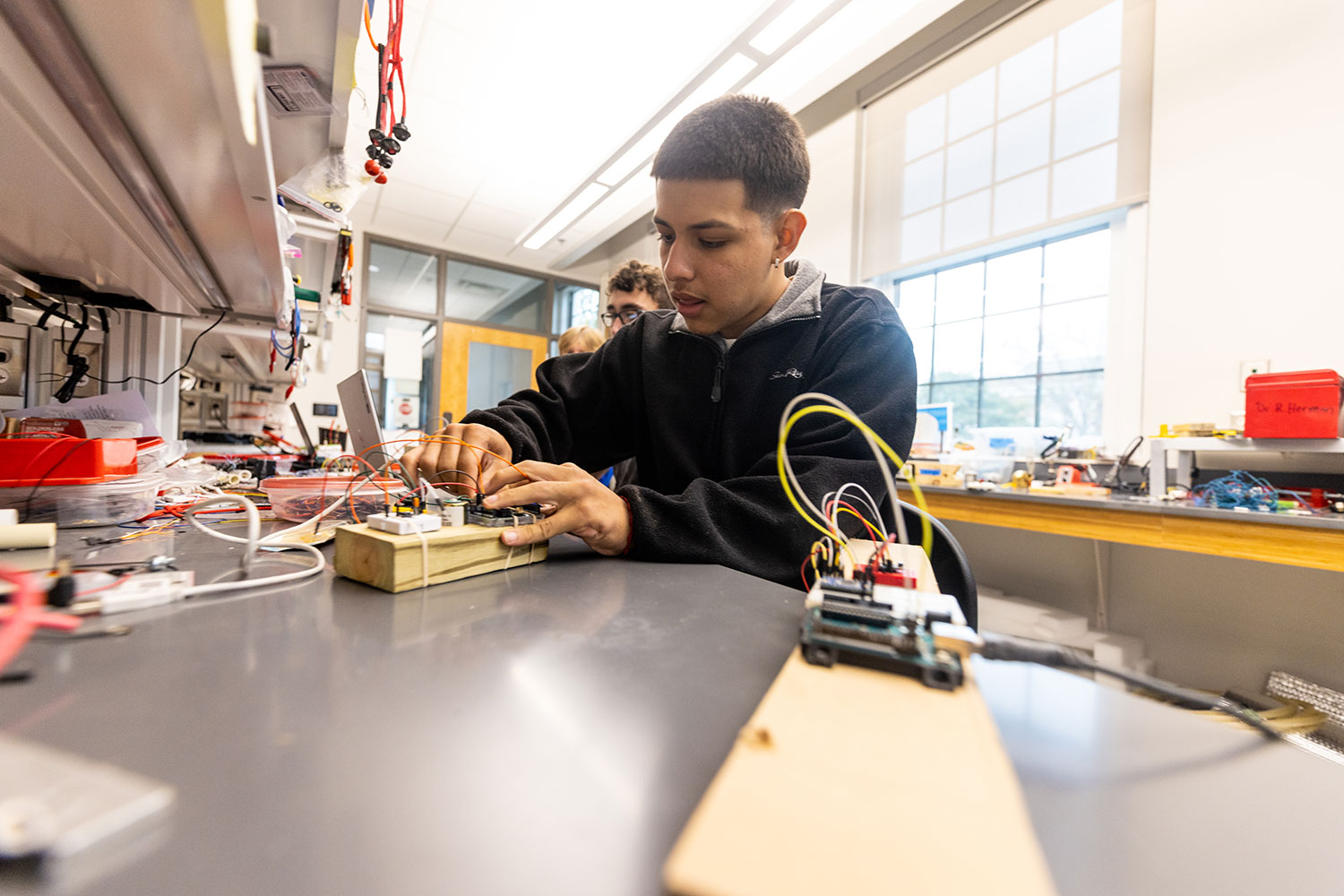
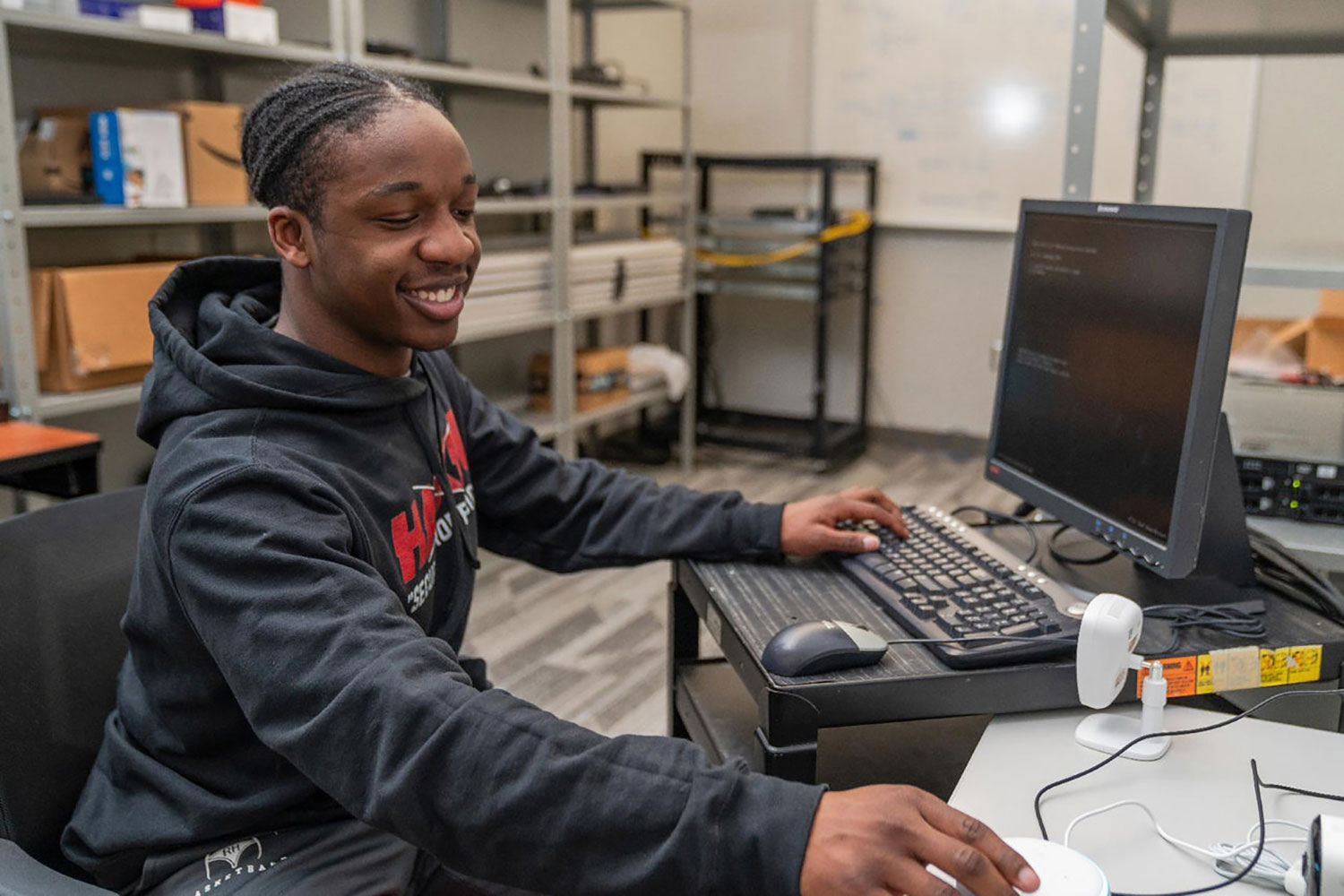
Breakthroughs in the science, technology, engineering and mathematics (STEM) fields are driving innovations that continuously transform our daily lives.
With this in mind, we prepare our students for successful careers in the STEM fields while actively engaging in real-world problem-solving.
Student Spotlight
Committees, Centers and Museums
The Artis College of Science and Technology at Radford University is home to a wide range of unique facilities that fosters curiosity, discovery, and practical experience across multiple scientific disciplines.
Academic Departments and School
News
-
Radford students preparing for spring break trip to explore, research national parks in western U.S.
February 25, 2026
A group of Radford students are getting a unique opportunity to explore and conduct research at national parks.

-
Highlander Highlights: Week of Feb. 9, 2026
February 13, 2026
Highlander Highlights shares with readers some of the extraordinary research and accomplishments happening on and off campus through the tireless work and curiosity of our students, staff, alumni and faculty.

-
Geospatial science major finds her place through Honors College, research and internships
January 15, 2026
Kayla Fields is gaining hands-on research experience examining water quality in the Chesapeake Bay.