Radford University
Artis College of Science and Technology
Innovation and Discovery

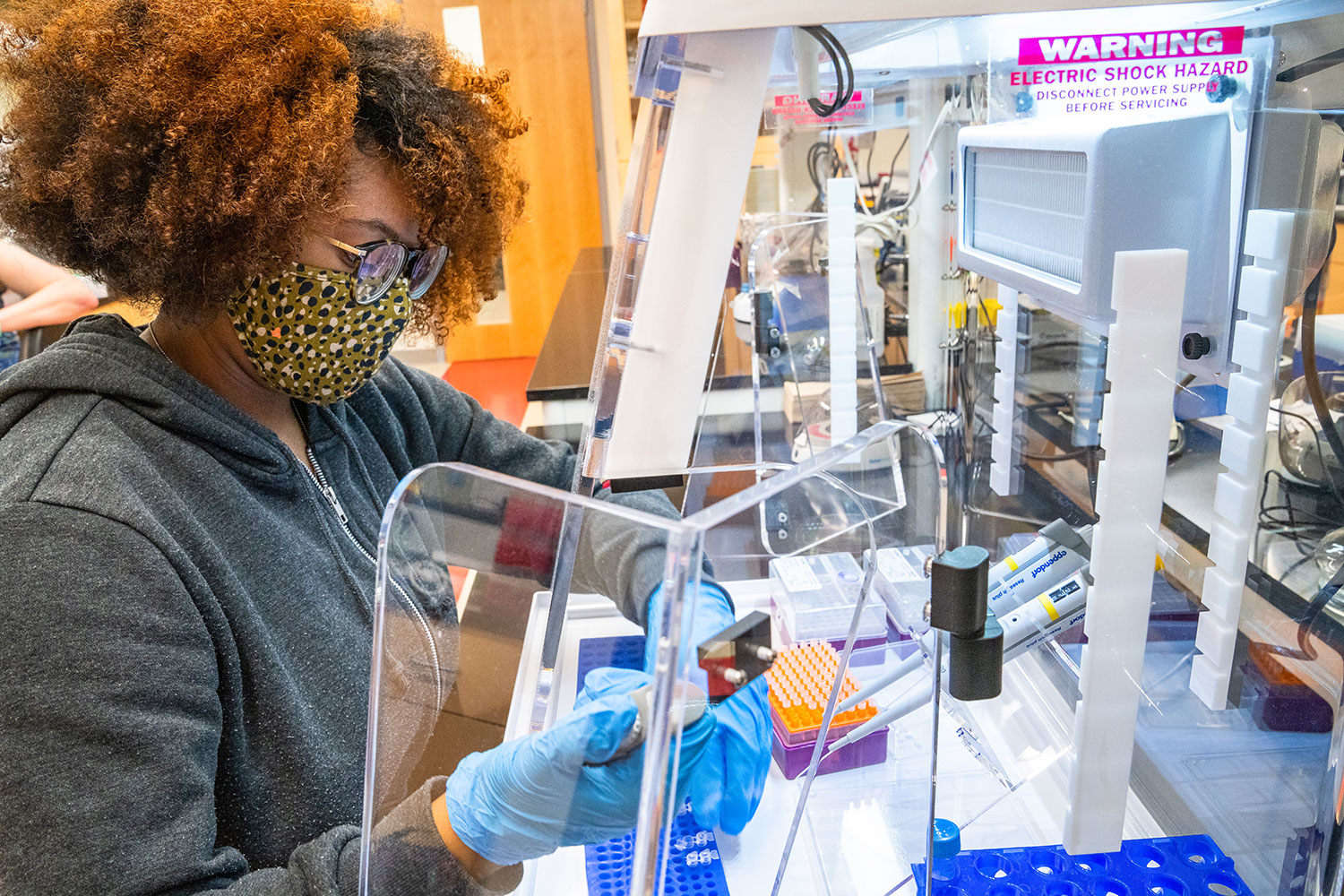
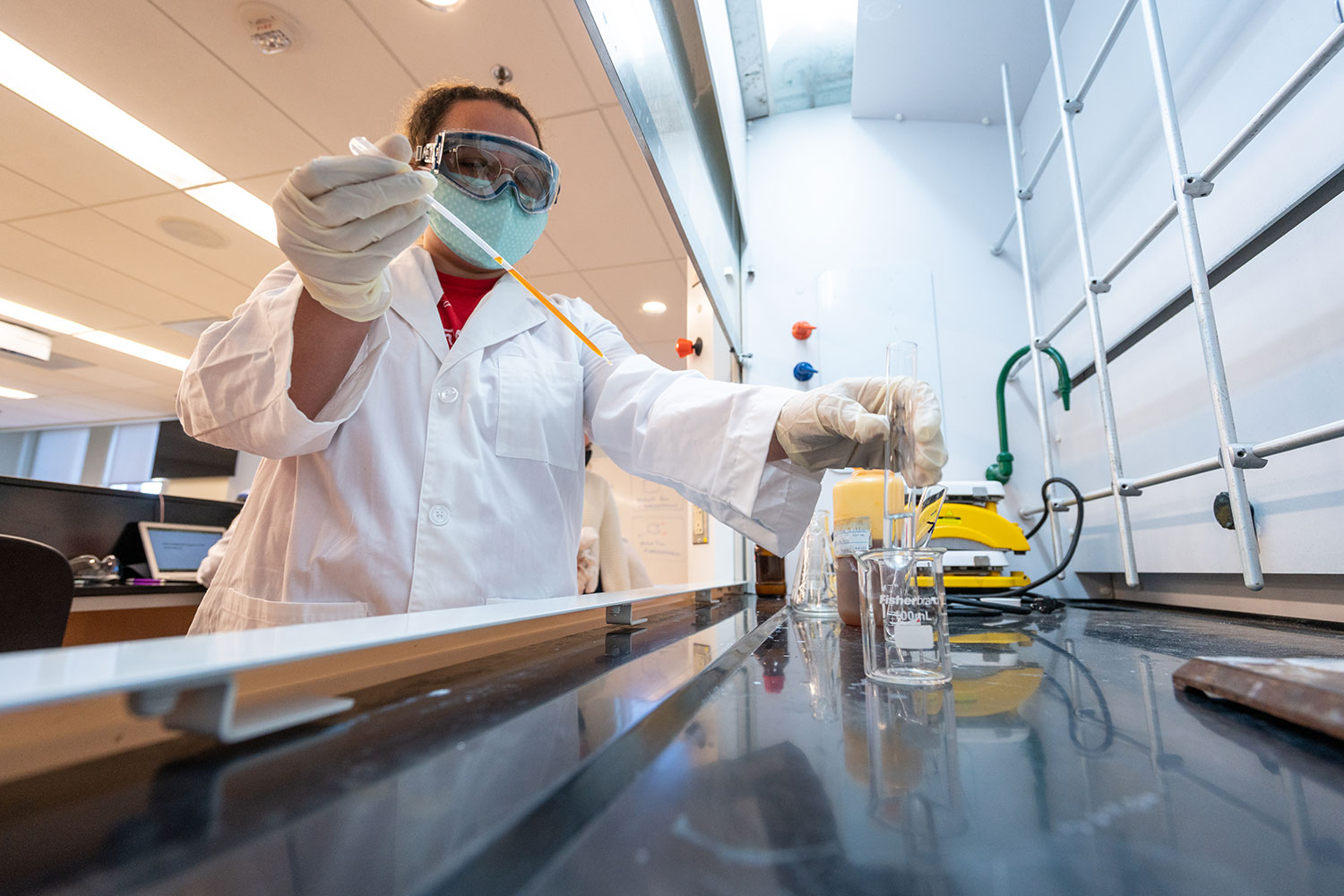
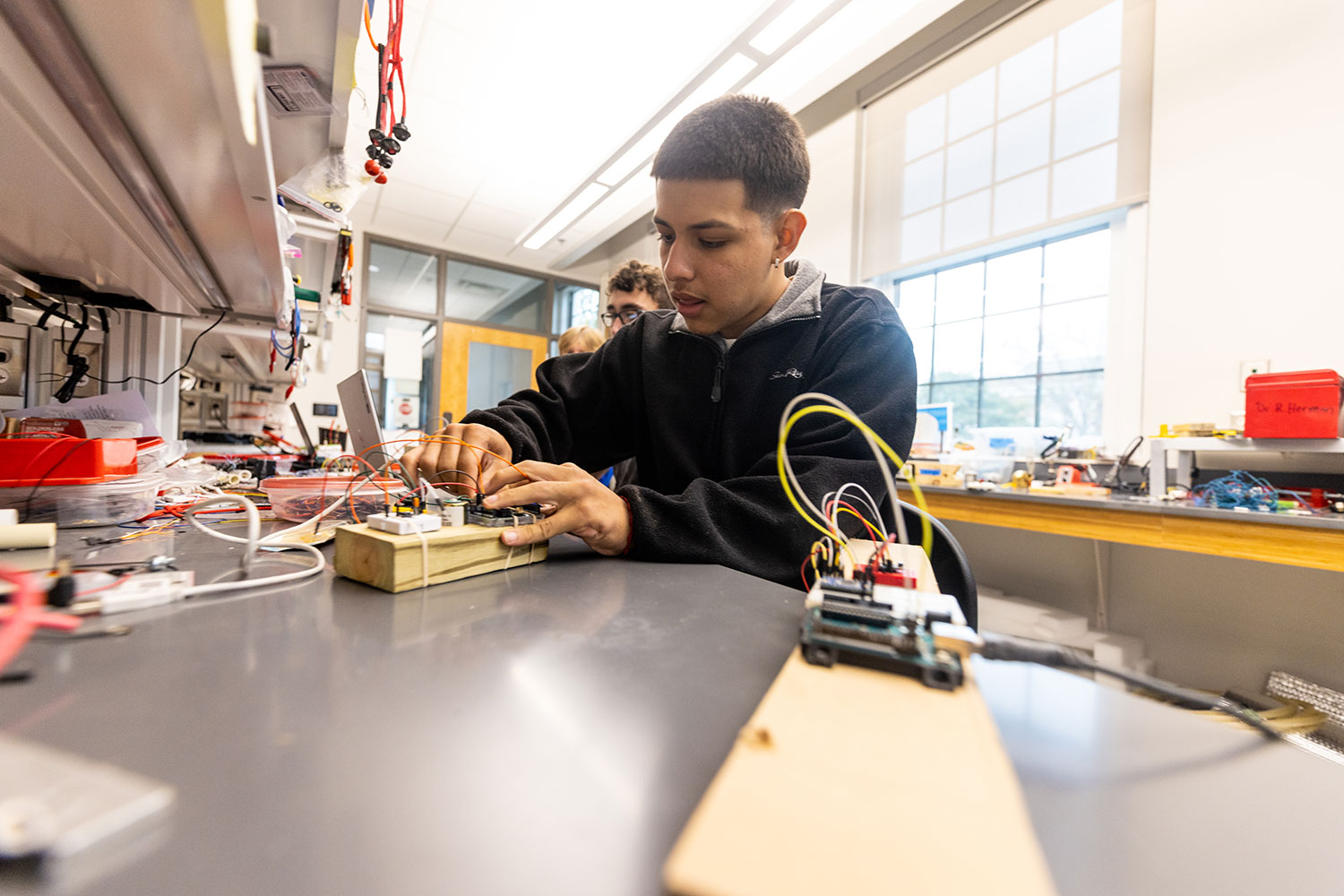
Breakthroughs in the science, technology, engineering and mathematics (STEM) fields are driving innovations that continuously transform our daily lives.
With this in mind, we prepare our students for successful careers in the STEM fields while actively engaging in real-world problem-solving.
Student Spotlight
Committees, Centers and Museums
The Artis College of Science and Technology at Radford University is home to a wide range of unique facilities that fosters curiosity, discovery, and practical experience across multiple scientific disciplines.
Academic Programs and School
News
-
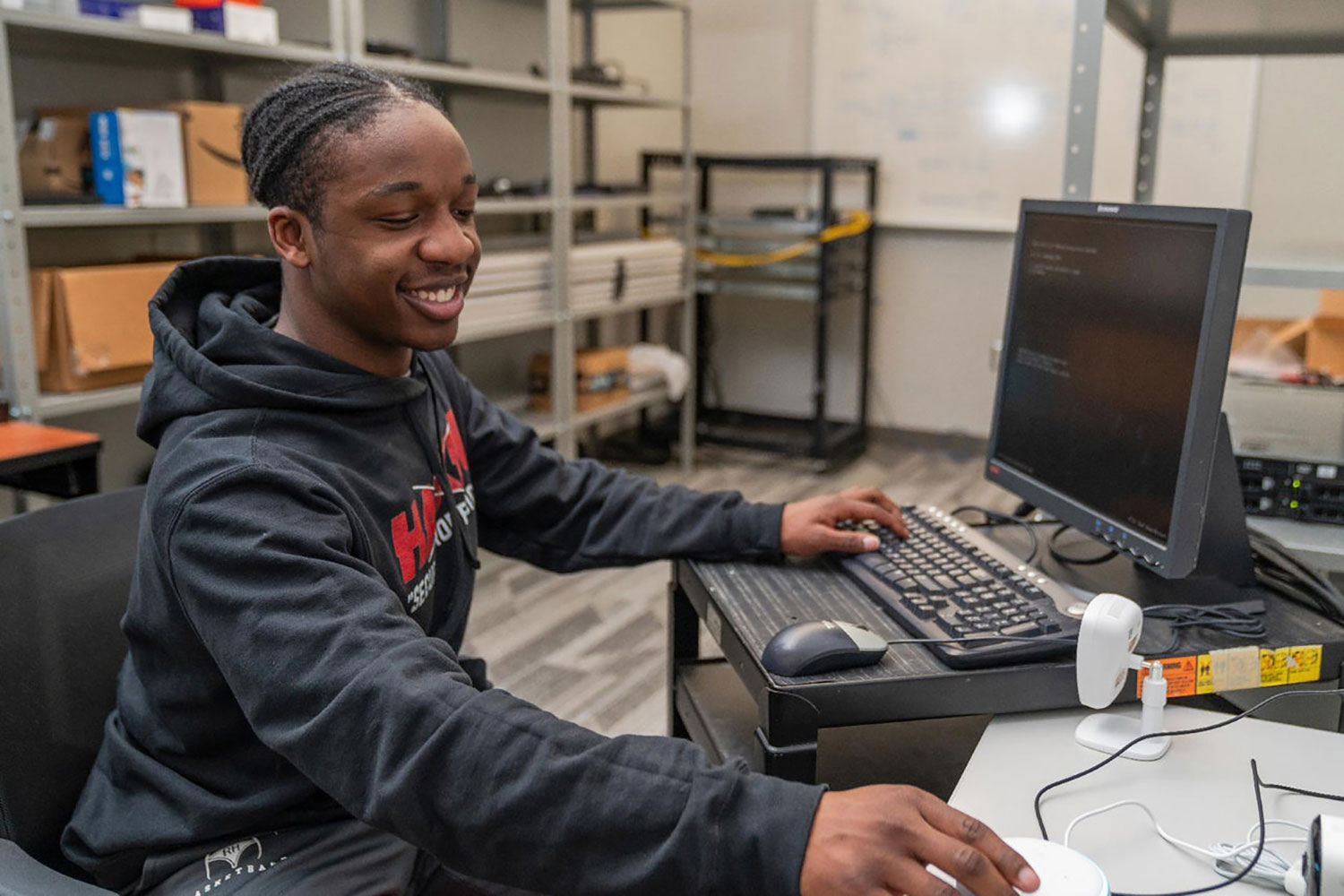
Walking around inside his mother’s house, Sam Williams ’25 uttered a sentence you don’t often hear: “I’m excited to wake up every day thinking about hacking."

-
Academic, campus enhancements and student success among June Board of Visitors meeting topics
June 10, 2025
Radford University’s Board of Visitors approved new programs and measures designed to move the institution forward and received updates on student success initiatives and campus enhancements during the final quarterly meetings of the academic year on Thursday and Friday, June 5-6.

-
Radford University has been awarded a $1,299,570 grant from the Commonwealth of Virginia as part of the Pell Initiative for Virginia, a new statewide effort to help more students from low-income backgrounds attend college, stay enrolled and graduate.